Kong: Agentic Reverse Engineering
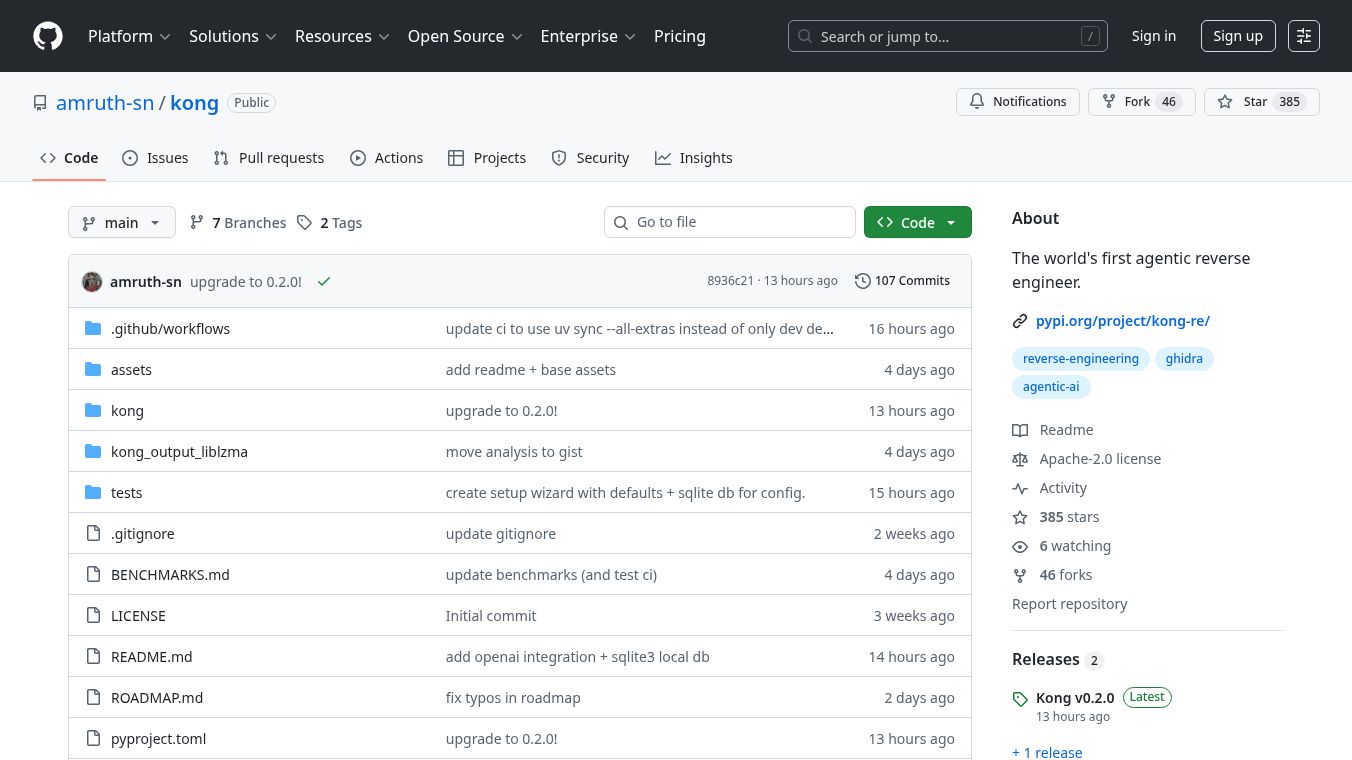
Kong is an AI-powered tool that helps with reverse engineering. This means it can analyze computer programs, especially those that have been made difficult to understand on purpose. Kong uses advanced AI, called Large Language Models or LLMs, to figure out what the program is doing, recover lost information like function names and data types, and rename parts of the code. This makes the process much faster and easier than doing it by hand.
Many programs, when they are prepared for distribution, have their helpful names and descriptions removed. This makes them hard to read and understand for security researchers or developers who need to examine them. Kong solves this by gathering a lot of information about the program from a tool called Ghidra. It then gives this information to an LLM, which can use the context to provide more accurate analysis and help remove confusing code.
Benefits
Kong offers several advantages. It has a fully automatic process that can analyze a program from start to finish with just one command. It works directly with Ghidra's analysis engine, which makes it efficient. Kong analyzes functions in a smart order, making sure that functions called by others are understood first. It provides LLMs with detailed context about functions, not just the basic code. After analysis, it cleans up naming and fixes inconsistencies. It can also identify common library functions quickly. Kong is designed to find and remove common code hiding techniques. It even has a way to check how accurate its analysis is by comparing it to the original source code. It supports different AI models like those from Anthropic and OpenAI and keeps track of costs.
Use Cases
Kong can be used to analyze programs written in languages like C, C++, Go, and Rust, and it supports various computer architectures. The tool follows a clear five-step process: Triage, Analysis, Cleanup, Synthesis, and Export. The analysis step is particularly powerful because it works from the bottom up and can remove tricky code obfuscation.
Vibes
Kong is licensed under the Apache License 2.0, which allows for commercial use. The project welcomes feedback and contributions from users.
This content is either user submitted or generated using AI technology (including, but not limited to, Google Gemini API, Llama, Grok, and Mistral), based on automated research and analysis of public data sources from search engines like DuckDuckGo, Google Search, and SearXNG, and directly from the tool's own website and with minimal to no human editing/review. THEJO AI is not affiliated with or endorsed by the AI tools or services mentioned. This is provided for informational and reference purposes only, is not an endorsement or official advice, and may contain inaccuracies or biases. Please verify details with original sources.


Comments
Please log in to post a comment.